The newest registered user is mark5
Our users have posted a total of 48861 messages in 7215 subjects

WORLD CLOCK
MICROSOFT PROBABLY HAS YOUR ENCRYPTION KEY
Valley of the Sun Casual Club :: TODAY'S TECHNOLOGY TIPS FROM THE DOCTOR OF TECHNOLOGY AZDEWARS 143 TOPICS inside
 MICROSOFT PROBABLY HAS YOUR ENCRYPTION KEY
MICROSOFT PROBABLY HAS YOUR ENCRYPTION KEY


azdewars
362 PostsFri, Jan 1 2016 3:28 AM
New Windows devices have disk encryption that is built-in and turned on by default, protecting your data in case your device is lost or stolen. But what is less well-known is that, if you are like most users and login to Windows 10 using your Microsoft account, your computer automatically uploaded a copy of your recovery key — which can be used to unlock your encrypted disk — to Microsoft’s servers, probably without your knowledge and without an option to opt out.
During the “crypto wars” of the ’90s, the National Security Agency developed an encryption backdoor technology — endorsed and promoted by the Clinton administration — called the Clipper chip, which it hoped telecom companies would use to sell backdoored crypto phones. Essentially, every phone with a Clipper chip would come with an encryption key, but the government would also get a copy of that key — this is known as key escrow — with the promise to only use it in response to a valid warrant. But due to public outcry and the availability of encryption tools like PGP, which the government didn’t control, the Clipper chip program ceased to be relevant by 1996. (Today, most phone calls still aren’t encrypted. You can use the free, open source, backdoorlessSignal app to make encrypted calls.)
The fact that new Windows devices require users to backup their recovery key on Microsoft’s servers is remarkably similar to a key escrow system, but with an important difference. Users can choose to delete recovery keys from their Microsoft accounts (you can skip to the bottom of this posting to learn how) — something that people never had the option to do with the Clipper chip system. But they can only delete it after they’ve already uploaded it to the cloud.
“The gold standard in disk encryption is end-to-end encryption, where only you can unlock your disk. This is what most companies use, and it seems to work well. There are certainly cases where it’s helpful to have a backup of your key or password. In those cases you might opt in to have a company store that information. But handing your keys to a company like Microsoft fundamentally changes the security properties of a disk encryption system.
As soon as your recovery key leaves your computer, you have no way of knowing its fate. A hacker could have already hacked your Microsoft account and can make a copy of your recovery key before you have time to delete it. Or Microsoft itself could get hacked, or could have hired a rogue employee with access to user data. Or a law enforcement or spy agency could send Microsoft a request for all data in your account, which would legally compel it to hand over your recovery key, which it could do even if the first thing you do after setting up your computer is delete it.
Your computer is now only as secure as that database of keys held by Microsoft, which means it may be vulnerable to hackers, foreign governments, and people who can extort Microsoft employees.
Of course, keeping a backup of your recovery key in your Microsoft account is genuinely useful for probably the majority of Windows users, which is why Microsoft designed the encryption scheme, known as “device encryption,” this way. If something goes wrong and your encrypted Windows computer breaks, you’re going to need this recovery key to gain access to any of your files. Microsoft would rather give their customers crippled disk encryption than risk their data.
When a device goes into recovery mode, and the user doesn’t have access to the recovery key, the data on the drive will become permanently inaccessible. Based on the possibility of this outcome and a broad survey of customer feedback we chose to automatically backup the user recovery key, The recovery key requires physical access to the user device and is not useful without it. After you finish setting up your Windows computer, you can login to your Microsoft account and delete the recovery key. Is this secure enough? If Microsoft doesn’t keep backups, maybe, but it’s hard to guarantee that. And for people who aren’t aware of the risk, opt-out seems risky.
This policy is in stark contrast to Microsoft’s major competitor, Apple. New Macs also ship with built-in and default disk encryption: a technology known as FileVault. Like Microsoft, Apple lets you store a backup of your recovery key in your iCloud account. But in Apple’s case, it’s an option. When you set up a Mac for the first time, you can uncheck a box if you don’t want to send your key to Apple’s servers.
This policy is also in contrast to Microsoft’s premium disk encryption product called BitLocker, which isn’t the same thing as what Microsoft refers to as device encryption. When you turn on BitLocker you’re forced to make a backup of your recovery key, but you get three options: Save it in your Microsoft account, save it to a USB stick, or print it.
To fully understand the different disk encryption features that Windows offers, you need to know some Microsoft jargon. Windows comes in different editions: Home (the cheapest), Pro, and Enterprise (more expensive). Windows Home includes device encryption, which started to become available during Windows 8, and requires your computer to have a tamper-resistant chip that stores encryption keys, something all new PCs come with. Pro and Enterprise both include device encryption, and they also include BitLocker, which started to become available during Windows Vista, but only for the premium editions. Under the hood, device encryption and BitLocker are the same thing. The difference is there’s only one way to use device encryption, but BitLocker is configurable.
If you’re using a recent version of Windows, and your computer has the encryption chip, and if you have a Microsoft account, your disk will automatically get encrypted, and your recovery key will get sent to Microsoft. If you login to Windows using your company’s or university’s Windows domain, then your recovery key will get sent to a server controlled by your company or university instead of Microsoft — but still, you can’t prevent device encryption from sending your recovery key. If you choose to not use a Microsoft or a domain account at all and instead create a “local only” account, then you don’t get disk encryption.
BitLocker, on the other hand, gives you more control. When you turn on BitLocker you get the choice to store your recovery key locally, among other options. But if you buy a new Windows device, even if it supports BitLocker, you’ll be using device encryption when you first set it up, and you’ll automatically send your recovery key to Microsoft.
In short, there is no way to prevent a new Windows device from uploading your recovery key the first time you log in to your Microsoft account, even if you have a Pro or Enterprise edition of Windows. And this is worse than just Microsoft choosing an insecure default option. Windows Home users don’t get the choice to not upload their recovery key at all. And while Windows Pro and Enterprise users do get the choice (because they can use BitLocker), they can’t exercise that choice until after they’ve already uploaded their recovery key to Microsoft’s servers.How to delete your recovery key from your Microsoft account
Go to this website and log in to your Microsoft account — this will be the same username and password that you use to log in to your Windows device. Once you’re in, it will show you a list of recovery keys backed up to your account.
If any of your Windows devices are listed, this means that Microsoft, or anyone who manages to access data in your Microsoft account, is technically able to unlock your encrypted disk, without your consent, as long as they physically have your computer. You can go ahead and delete your recovery key on this page — but you may want to back it up locally first, for example by writing it down on a piece of paper that you keep somewhere safe.
If you don’t see any recovery keys, then you either don’t have an encrypted disk, or Microsoft doesn’t have a copy of your recovery key. This might be the case if you’re using BitLocker and didn’t upload your recovery key when you first turned it on.
When you delete your recovery key from your account on this website, Microsoft promises that it gets deleted immediately, and that copies stored on its backup drives get deleted shortly thereafter as well. “The recovery key password is deleted right away from the customer’s online profile. As the drives that are used for failover and backup are sync’d up with the latest data the keys are removed,” a Microsoft spokesperson assured me.
If you have sensitive data that’s stored on your laptop, in some cases it might be safer to completely stop using your old encryption key and generate a new one that you never send to Microsoft. This way you can be entirely sure that the copy that used to be on Microsoft’s server hasn’t already been compromised.Generate a new encryption key without giving a copy to Microsoft
In order to generate a new disk encryption key, this time without giving a copy to Microsoft, you need decrypt your whole hard disk and then re-encrypt it, but this time in such a way that you’ll actually get asked how you want to backup your recovery key.
This is only possible if you have Windows Pro or Enterprise. Unfortunately, the only thing you can do if you have the Home edition is upgrade to a more expensive edition or use non-Microsoft disk encryption software, such asBestCrypt, which you have to pay for. You may also be able to get open source encryption software like VeraCrypt working, but sadly the open source options for full disk encryption in Windows don’t currently work well with modern PC hardware (as touched on here).
Go to Start, type “bitlocker,” and click “Manage BitLocker” to open BitLocker Drive Encryption settings.
From here, click “Turn off BitLocker.” It will warn you that your disk will get decrypted and that it may take some time. Go ahead and continue. You can use your computer while it’s decrypting.
After your disk is finished decrypting, you need to turn BitLocker back on. Back in the BitLocker Drive Encryption settings, click “Turn on BitLocker.”
It will check to see if your computer supports BitLocker, and then it will ask you how you want to backup your recovery key. It sure would be nice if it asked you this when you first set up your computer.
If you choose to save it to a file, it will make you save it onto a disk that you’re not currently encrypting, such as a USB stick. Or you can choose to print it and keep a hard copy. You must choose one of them to continue, but make sure you don’t choose “Save to your Microsoft account.”
On the next page it will ask you if you want to encrypt used disk space only (faster) or encrypt your entire disk including empty space (slower). If you want to be on the safe side, choose the latter. Then on the next page it will ask you if you wish to run the BitLocker system check, which you should probably do.
Finally, it will make you reboot your computer.
When you boot back up your hard disk will be encrypting in the background. At this point you can check your Microsoft account again to see if Windows uploaded your recovery key – it shouldn’t have.
Now just wait for your disk to finish encrypting. Congratulations: Your disk is encrypted and Microsoft no longer has the ability to unlock it.
Best of wishes,
John - azdewars
Delete
Edit
Reply
Send to Friend
Report Abuse

pdb1
10,256 PostsFri, Jan 1 2016 11:48 AM  azdewars:
azdewars:
your recovery key — which can be used to unlock your encrypted disk — to Microsoft’s servers, probably without your knowledge and without an option to opt out.
That's okay . I left the light on for them .
Delete
Edit
Reply
Send to Friend
Report Abuse

pdb1
10,256 PostsFri, Jan 1 2016 11:54 AM
USEFUL HIGHLIGHTS
 azdewars:
azdewars:How to delete your recovery key from your Microsoft account
Go to this website and log in to your Microsoft account — this will be the same username and password that you use to log in to your Windows device. Once you’re in, it will show you a list of recovery keys backed up to your account.
If any of your Windows devices are listed, this means that Microsoft, or anyone who manages to access data in your Microsoft account, is technically able to unlock your encrypted disk, without your consent, as long as they physically have your computer. You can go ahead and delete your recovery key on this page — but you may want to back it up locally first, for example by writing it down on a piece of paper that you keep somewhere safe. azdewars:
azdewars: azdewars:
azdewars:
If you choose to save it to a file, it will make you save it onto a disk that you’re not currently encrypting, such as a USB stick. Or you can choose to print it and keep a hard copy. You must choose one of them to continue, but make sure you don’t choose “Save to your Microsoft account.”Generate a new encryption key without giving a copy to Microsoft
In order to generate a new disk encryption key, this time without giving a copy to Microsoft, you need decrypt your whole hard disk and then re-encrypt it, but this time in such a way that you’ll actually get asked how you want to backup your recovery key.
This is only possible if you have Windows Pro or Enterprise. Unfortunately, the only thing you can do if you have the Home edition is upgrade to a more expensive edition or use non-Microsoft disk encryption software, such asBestCrypt, which you have to pay for. You may also be able to get open source encryption software like VeraCrypt working, but sadly the open source options for full disk encryption in Windows don’t currently work well with modern PC hardware (as touched on here).
Go to Start, type “bitlocker,” and click “Manage BitLocker” to open BitLocker Drive Encryption settings. azdewars:
azdewars:
When you boot back up your hard disk will be encrypting in the background. At this point you can check your Microsoft account again to see if Windows uploaded your recovery key – it shouldn’t have.
OR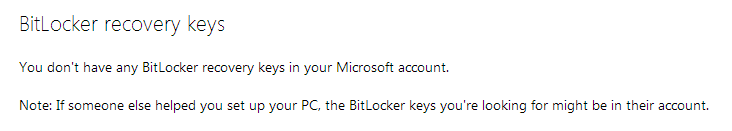
Delete
Edit
Reply
Send to Friend
Report Abuse

azdewars
362 PostsFri, Jan 1 2016 12:52 PM
Good point Paul. Sadly enough, thats a realistic situation,
John
Delete
Edit
Reply
Send to Friend
Report Abuse

Sage013
123 PostsFri, Jan 1 2016 10:11 PM
Alternatively you can just turn off the One Drive cloud storage by disabling it in "Services". .
.
There's plenty of cloud based storage options available out there as an alternative, and you'll probably find your ISP offers it for free. Not sure with desktop PC's but , Acer and Asus provide a free cloud storage service on their laptops.
Just make sure you read the small print on what security they are offering though.
I never store any personal data on any device I have that I would worry about someone else seeing. That way I have nothing to lose. :P
Paul
Please enjoy
_________________
May the SUN always be with you
home of
https://www.valleyofthesuncc.com/ an information and entertainment only website
 Similar topics
Similar topics» Windows 10: Microsoft's first MAJOR update is coming NEXT WEEK
» Google, Microsoft, Netflix & More Join Forces For New Video Format
Valley of the Sun Casual Club :: TODAY'S TECHNOLOGY TIPS FROM THE DOCTOR OF TECHNOLOGY AZDEWARS 143 TOPICS inside

 Events
Events































































» Disneyland vacation
» UP & COMERS
» WGT POETRY , QUOTES , MOMENTS , & MORE
» Word Genius Word of the day * Spindrift *
» Tales of Miurag #3 in Paperback Patreon Story in December!
» Download WhatsApp
» WORD DAILY Word of the Day: * Saponaceous *
» Word Genius Word of the day * Infracaninophile *
» THE TRUMP DUMP .....
» INTERESTING FACTS * How do astronauts vote from space? *
» WWE Crown Jewel is almost here! Don't miss the action LIVE today only on Peacock!
» NEW GUEST COUNTER
» Merriam - Webster Word of the day * ‘Deadhead’ *
» WWE Universe: Your Crown Jewel Broadcast Schedule has arrived!